Modern financial ecosystems face a daunting reality where a single line of corrupted code in a remote server can paralyze global transactions within seconds. The Financial Conduct Authority (FCA) has recently overhauled its regulatory framework to address this vulnerability, shifting the focus from simple compliance to true operational resilience. This evolution forces a critical comparison between internal cyber incident reporting and the management of Third-Party Risk Management (TPRM). While both aim to protect the market, they function as two distinct gears in the same defensive machine.
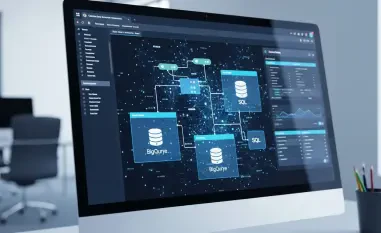
Financial institutions now navigate a landscape where Cloud Service Providers (CSPs) and digital supply chains are as integral as their own core banking systems. The FCA updates move beyond reactive measures, establishing a dual-track strategy that balances immediate internal transparency with long-term external vendor accountability. Understanding how these components interact is essential for any firm attempting to maintain stability in an increasingly interconnected and volatile digital economy.
Key Performance Indicators and Regulatory Benchmarks
Speed and Transparency of Incident Notifications
The FCA mandate demands an unprecedented level of immediacy for internal cyberattack reporting, requiring firms to disclose system failures almost as they occur. This pressure for transparency ensures that the regulator can spot systemic trends before they snowball into industry-wide crises. By standardizing reporting categories, the FCA has effectively removed the ambiguity that once allowed firms to downplay the severity of a breach or technical glitch.
In contrast, visibility into third-party disruptions remains a significant hurdle. While internal teams are under strict regulatory clocks, external vendors often operate under varied Service Level Agreements (SLAs) that might not align with FCA expectations. This creates a dangerous information gap where an institution knows its systems are failing but lacks the immediate data from its provider to explain why, complicating the initial response phase.
Accountability and Oversight in External Partnerships
A fundamental pillar of the updated guidelines is the non-delegable nature of responsibility; a firm can outsource its data storage to the cloud, but it cannot outsource its regulatory accountability. Financial institutions must now implement rigorous oversight mechanisms to monitor their partners. This involves technical audits and real-time performance tracking to ensure that a provider’s security posture matches the bank’s own internal standards.
Managing vulnerabilities within the digital supply chain requires a different technical lens than internal defense. While internal risks are often mitigated through direct administrative controls, external risks demand complex contract management and contingency planning. The FCA emphasizes that reliance on a single major CSP creates a “single point of failure” risk, making the diversification of digital partnerships a critical metric for long-term survival.
Data Integrity and Consumer Protection Metrics
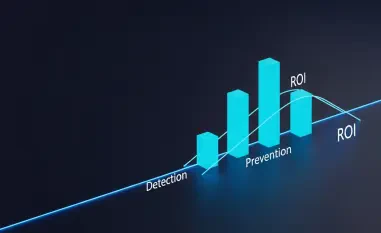
Cyber reporting serves as a form of collective defense, where shared intelligence allows the FCA to broadcast warnings about emerging threats to the entire sector. This shared knowledge base turns individual failures into industry-wide lessons, directly safeguarding market integrity. It transforms the concept of reporting from a burdensome chore into a strategic contribution to the financial system’s overall health.
However, dependencies on third-party services often create silos where risk is hidden behind proprietary vendor walls. If a major provider suffers a silent degradation of data integrity, the downstream effects on consumer protection can be catastrophic before they are even detected. Standardized metrics are therefore being pushed onto these vendors to ensure that the “black box” of third-party operations becomes more transparent to the institutions they serve.
Practical Challenges in Regulatory Compliance and Vendor Management
Categorizing complex incidents under the new streamlined FCA processes remains technically difficult for many legacy institutions. When a hybrid cloud environment suffers a partial outage, determining whether the root cause is an internal configuration error or a vendor-side failure takes time that the regulator’s clock does not afford. This creates a high-pressure environment where accuracy and speed are frequently at odds.
Logistically, maintaining oversight over global cloud giants presents a David-and-Goliath scenario for smaller financial firms. These institutions often lack the leverage to demand bespoke security audits from massive service providers. Consequently, they are forced to rely on generic compliance reports, which may not fully capture the specific risks inherent in their unique digital supply chain configurations.
Strategic Recommendations for Financial Institutions
The transition toward a standardized reporting environment has fundamentally shifted the baseline for financial stability. Firms must now prioritize the integration of advanced third-party risk monitoring tools that provide real-time telemetry, rather than relying on annual questionnaires. Moving toward automated, proactive vendor auditing allowed organizations to identify weaknesses in the supply chain long before they escalated into reportable incidents.
Integrating FCA compliance into a unified resilience strategy proved to be the most effective way to mitigate both internal and external threats. Leaders who treated regulatory notifications as a strategic data asset, rather than a legal hurdle, gained better internal buy-in for security investments. Ultimately, the industry moved toward a model where transparency with the regulator and accountability for vendors were viewed as two sides of the same coin, ensuring that operational resilience remained a lived reality rather than just a policy goal.