Modern network security is no longer defined solely by the strength of the perimeter but by the resilience of the central orchestration engines that manage global data flows. Recent disclosures regarding the Cisco Catalyst SD-WAN Manager have sent shockwaves through the enterprise sector as threat actors pivot toward these high-value controllers. This roundup examines the multifaceted nature of these attacks, drawing on security advisories and forensic observations to provide a comprehensive look at the risks facing today’s software-defined architectures.
The Rising Stakes of Infrastructure Exploitation in Enterprise Networking
The shift from targeting individual workstations to weaponizing core networking hardware like the Catalyst SD-WAN Manager represents a significant evolution in cyber warfare. As organizations have migrated from the legacy vManage system to the more integrated Catalyst ecosystem, these central controllers have become the ultimate “crown jewels” for advanced persistent threats. A compromise at this level does not just affect a single user; it grants an adversary influence over the entire fabric of an organization’s wide-area network.
The current threat landscape demonstrates that even vulnerabilities with moderate severity ratings are being chained together to bypass sophisticated corporate defenses. This trend suggests that attackers are no longer waiting for a “perfect” zero-day exploit. Instead, they are methodically deconstructing the administrative interfaces of infrastructure platforms to find combinations of flaws that, while minor in isolation, provide a path to full system takeover when executed in a specific sequence.
Analyzing the Mechanics and Impact of Active SD-WAN Exploitation
Dissecting the CVE-2026-20122 and CVE-2026-20128 Vulnerability Chain
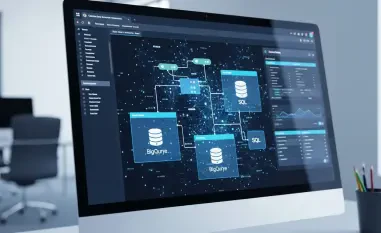
At the heart of the recent surge in activity is a potent combination of arbitrary file overwrites and privilege escalation. CVE-2026-20122 allows an authenticated attacker with limited API access to modify local system files, while CVE-2026-20128 enables the elevation of permissions to those of a Data Collection Agent. When used in tandem, these flaws allow an intruder to move from a restricted observer role to a position where they can alter the foundational configuration of the SD-WAN environment.
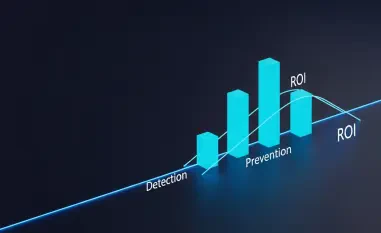
The deceptive nature of CVSS scores is on full display here, as the 7.1 and 5.5 ratings might lead some teams to delay patching. However, in a live attack scenario, these numbers fail to capture the lethal potential of a chain that effectively grants administrative control. Detecting these incidents is particularly difficult because the traffic often mimics legitimate administrative API calls, allowing malicious actions to blend into the daily noise of network management.
The UAT-8616 Threat Profile and the Global Surge in Scanning Activity
A specific threat actor, identified as UAT-8616, has been linked to the aggressive deployment of web shells across compromised perimeters. Telemetry data indicates a massive spike in opportunistic scanning, with a significant peak of activity recorded on March 4. This actor appears to prioritize breadth over depth, launching mass-scale exploitation attempts that target systems across the United States and other key economic regions to establish as many persistent footholds as possible.
This shift toward automated, large-scale exploitation marks a departure from surgical strikes. By casting a wide net, UAT-8616 and similar groups can identify unpatched systems before IT departments have a chance to implement fixes. The speed at which these vulnerabilities are being weaponized underscores the reality that the window between the disclosure of a flaw and its active exploitation has effectively vanished.
Compounding Risks: The Shadow of Maximum-Severity Firewall Flaws
The risks to the SD-WAN environment are further compounded by critical flaws in the Secure Firewall Management Center, such as CVE-2026-20079 and CVE-2026-20131. These vulnerabilities allow for unauthenticated root access and the execution of arbitrary Java code, creating a nightmare scenario for security teams. If an attacker gains control of the firewall management layer, they can essentially blind the organization’s security stack, making the subsequent SD-WAN compromise even harder to detect.
These “manager-of-managers” platforms have inadvertently become single points of failure. When the very tools designed to secure and orchestrate the network are themselves vulnerable, the traditional assumption of perimeter security is rendered obsolete. This interconnected risk profile means that a single oversight in one management interface can lead to a cascading failure across the entire software-defined infrastructure.
The Forensic Reality of a Compromised SD-WAN Environment
Identifying unauthorized persistence after a successful file overwrite is a grueling forensic task. Once an attacker has modified local system files, they can hide their presence within legitimate processes, making standard detection tools less effective. Security professionals now warn that the risk of long-term lateral movement within the network fabric is just as dangerous as immediate data exfiltration, as it allows attackers to maintain access for months or even years.
Because of the depth of access provided by these exploits, any unpatched system exposed to the internet during the peak attack window should be treated with a “presumed breach” mentality. This requires a shift from simple remediation to a full-scale incident response, involving thorough log audits and the verification of system integrity. The goal is to ensure that no dormant web shells or backdoors remain within the environment after the initial patches are applied.
Strategic Remediation and Hardening the SD-WAN Control Plane
The primary line of defense involves a rigorous patch management lifecycle for Catalyst SD-WAN versions 20.9 through 20.18. Organizations must prioritize these updates to neutralize known exploit vectors immediately. However, patching is only the first step; a true defense-in-depth strategy requires transitioning all administrative access to HTTPS-only and decommissioning legacy services like FTP that offer unnecessary attack surfaces.
Beyond technical updates, administrators should implement granular API permissions to ensure that even a compromised set of credentials cannot be used to execute high-privilege commands. Continuous log monitoring and behavioral analysis are also essential. By establishing a baseline of normal administrative behavior, teams can more easily spot the subtle indicators of compromise, such as unusual file modifications or API calls originating from unexpected geographic locations.
Navigating the Future of Secure Network Orchestration
The recent wave of attacks against Cisco’s infrastructure demonstrated the critical need for a more proactive approach to network maintenance. IT departments successfully mitigated many risks by treating networking patches with the same level of urgency as operating system zero-days. This proactive stance was essential in preventing large-scale data theft and maintaining the integrity of corporate communications during a period of intense adversarial pressure.
Looking forward, the focus shifted toward a permanent “zero trust” posture for all administrative interfaces. Organizations began isolating management consoles from the public internet entirely, utilizing dedicated management networks and multi-factor authentication for every access point. These measures proved vital in building long-term resilience, ensuring that even if a new vulnerability were discovered, the overall impact on the organizational fabric remained contained and manageable.