Introduction to Endpoint Security and Arctic Wolf’s Role
In an era where cyber threats loom larger than ever, with global cybercrime costs projected to reach staggering heights, endpoint security stands as a critical line of defense for organizations worldwide. Every device connected to a network represents a potential entry point for malicious actors, making robust protection not just a luxury but a necessity. The rapid shift to remote work and cloud-based systems has only intensified the urgency for solutions that can safeguard endpoints against increasingly sophisticated attacks.
Endpoint security, at its core, focuses on protecting devices like laptops, desktops, and mobile units from threats such as malware, ransomware, and phishing attempts. As digital transformation accelerates, the industry faces mounting pressure to deliver tools that can keep pace with evolving risks while maintaining user productivity. This challenge has spurred innovation, with companies striving to balance comprehensive defense mechanisms against the need for seamless system performance.
Arctic Wolf, recognized as a global leader in security operations, has emerged as a key player in this space with its cutting-edge offerings. Among its portfolio, Aurora Endpoint Security stands out as a flagship solution designed to address the complexities of modern cyber threats. By integrating advanced technologies, Arctic Wolf aims to set a new benchmark in how organizations protect their digital assets, ensuring both resilience and efficiency in an ever-changing threat landscape.
Tolly Group Evaluation: Unveiling Aurora’s Perfect Score
Testing Methodology and Key Metrics
An independent evaluation conducted by The Tolly Group, a trusted name in IT product validation, recently put Aurora Endpoint Security to the test on Windows 11 systems. The assessment centered on the solution’s ability to detect and neutralize threats using a sample set of 1,000 recent malware variants sourced from prominent public repositories. This rigorous process aimed to simulate real-world conditions that organizations face daily.
The methodology focused on critical performance indicators such as the threat detection rate, which measures the percentage of malicious entities successfully identified and blocked. Additionally, the evaluation tracked CPU resource utilization during scans to gauge the solution’s impact on system performance. These metrics provided a comprehensive view of how well the tool could protect without overburdening the devices it safeguards.
By establishing a clear framework for analysis, The Tolly Group ensured that the results would reflect both the effectiveness and practicality of Aurora Endpoint Security in operational environments. This approach highlights the importance of testing solutions under conditions that mirror the challenges faced by IT teams managing diverse and dynamic networks.
Results and Performance Highlights
The findings from the evaluation were nothing short of remarkable, with Aurora Endpoint Security achieving a perfect 100% threat protection rate against the tested malware samples. This achievement underscores the solution’s ability to identify and block threats with unparalleled precision. Such a result is rare in the industry, where even small gaps in detection can lead to significant vulnerabilities.
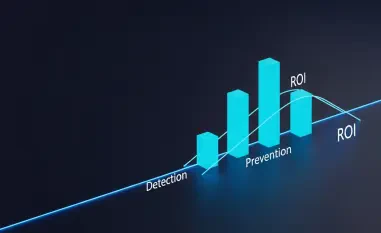
Equally impressive was the efficiency demonstrated during the testing process, as the solution utilized only about 33% of CPU resources compared to industry benchmarks that often demand nearly double that amount. This low resource footprint means that endpoint devices can maintain optimal performance, even during intensive security scans, avoiding the slowdowns that plague many competing products.
These results position Aurora Endpoint Security as a leader in delivering robust protection without compromising on system speed or user experience. The balance struck between efficacy and minimal impact offers a compelling case for organizations seeking to fortify their defenses while preserving operational continuity.
Challenges in Endpoint Security and Aurora’s Solutions
Endpoint security faces persistent hurdles, including the delicate act of providing ironclad protection without dragging down device performance. Many solutions struggle to keep up with the sheer volume and complexity of threats, especially in environments where devices operate across varied networks or in remote settings. This often results in trade-offs that can frustrate end-users and strain IT resources.
Aurora Endpoint Security tackles these issues head-on with innovative features tailored to modern needs. Its ability to perform offline detection ensures that devices remain protected even when disconnected from central networks, a crucial advantage for remote workers or operational technology setups. Furthermore, the solution’s design prioritizes early-stage threat blocking, stopping attacks before they can escalate into full-blown breaches.
By maintaining low resource usage, Aurora minimizes disruptions to daily operations, addressing a common pain point in endpoint defense. This focus on efficiency, paired with its capacity to handle diverse and complex threat landscapes, demonstrates a forward-thinking approach to overcoming the limitations that have long hindered the industry.
Key Features Driving Aurora’s Edge in Cybersecurity
Aurora Endpoint Security distinguishes itself through a suite of advanced capabilities that align with the pressing demands of cybersecurity today. One standout feature is its prowess in halting multi-stage cyberattacks, identifying and neutralizing threats at their inception. This proactive stance prevents the cascading damage that often follows sophisticated attacks.
Another critical strength lies in its offline protection mechanism, which ensures continuous security for devices regardless of connectivity status. Additionally, the integration of an AI assistant enhances the experience for security analysts by offering contextual insights and mappings to the MITRE ATT&CK framework, streamlining the process of threat analysis without reliance on external resources.
These elements collectively make Aurora a user-friendly and comprehensive endpoint detection and response solution. By addressing both technical and operational needs, the tool not only protects but also empowers teams to manage risks effectively, reflecting a deep understanding of the evolving requirements within the cybersecurity domain.
Industry Trends and Future Directions in Endpoint Security
The endpoint security sector is witnessing a surge in demand for solutions that deliver high protection levels while preserving system performance and employee productivity. Organizations are increasingly wary of tools that, while effective against threats, bog down operations or require extensive manual oversight. This trend underscores a shift toward streamlined, efficient technologies.
Looking ahead, the role of artificial intelligence in endpoint security is poised to grow, offering predictive capabilities and automated responses to emerging dangers. The industry must also adapt to the rise of remote work and the unique challenges posed by operational technology environments, where connectivity and security needs differ vastly from traditional office setups.
As cyber threats continue to evolve in complexity from this year through 2027, the emphasis will likely remain on developing adaptable solutions that can anticipate risks rather than merely react to them. Innovations in endpoint security will need to prioritize integration and scalability to support organizations navigating an increasingly distributed digital landscape.
Conclusion: Aurora’s Benchmark in Endpoint Protection
The independent evaluation by The Tolly Group marked a significant milestone, as Aurora Endpoint Security demonstrated a flawless 100% threat protection rate alongside exceptional efficiency in resource usage. This outcome not only validated the solution’s capabilities but also highlighted its potential to redefine standards in endpoint defense.
Moving forward, the industry could take inspiration from such achievements to drive innovation in creating tools that seamlessly integrate protection with performance. Organizations are encouraged to explore solutions like Aurora that prioritize both security and usability, ensuring they stay ahead of threats without sacrificing operational agility.
As a next step, stakeholders across the sector should consider investing in technologies that offer scalability and adaptability to meet future challenges. By focusing on comprehensive, efficient endpoint security, businesses position themselves to navigate the complexities of cyber risks with greater confidence and resilience.