
Olivia Martainz
Security ConsultantOlivia Martainz helps organizations compile comprehensive enterprise security protocols. She shares his expertise with a global audience and provides real-world examples to help readers better understand the complexities of cybersecurity. Olivia covers endpoint detection and response solutions, zero-trust security principles, and emerging threats in enterprise security.
With a deep background in threat intelligence and corporate security, Malik Haidar has spent his career on the front lines, dissecting the anatomy of sophisticated cyberattacks. Today, he joins us to unravel a particularly alarming campaign where a nation-state actor, UNC6201, exploited a
Vast troves of today's most sensitive encrypted data are being systematically stolen and stockpiled, not for immediate use, but to be unlocked by a key that does not yet exist. This strategy, known as "harvest now, decrypt later," represents a paradigm shift in data security, where

The digital ramparts protecting a nation's most sensitive information are not built of stone but of code, policy, and human vigilance, a reality that places Australia at a critical juncture in its ongoing cyber security campaign. Recent comprehensive assessments of the Commonwealth's

The digital extortion that once locked personal photos for a few hundred dollars has metastasized into a sophisticated criminal enterprise capable of bringing global supply chains to a standstill, demanding multi-million-dollar payments from the world’s largest corporations. This dramatic t

The long-standing reliance on physical keys and plastic cards for securing our spaces is rapidly giving way to a more integrated, intelligent, and fluid approach centered on the one device nearly everyone carries. Mobile-Based Access Control represents a significant advancement in the security and

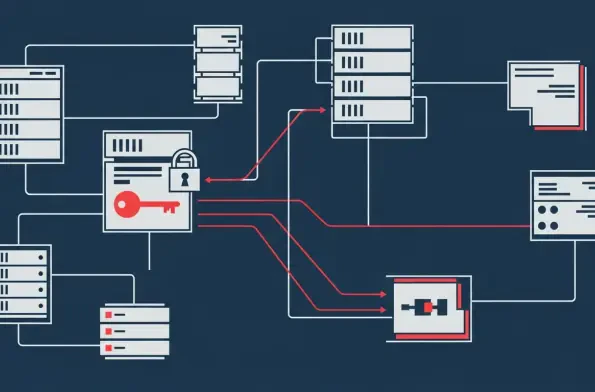
In the ever-evolving landscape of cybercrime, a particularly insidious threat has emerged that forgoes the noisy disruption of ransomware in favor of a silent, calculated theft designed to hold a company’s reputation hostage. A new malware variant, dubbed RustyRocket, is now at the center of a s

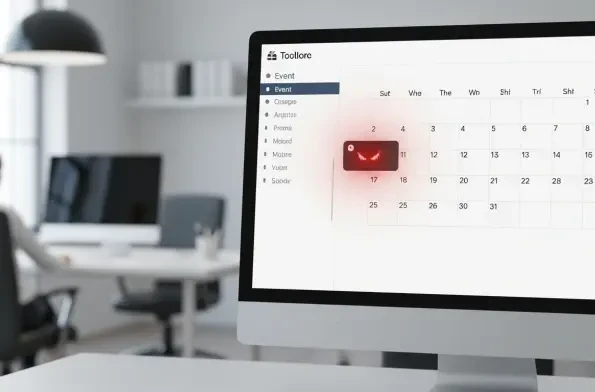
A seemingly innocent calendar notification pops up, but behind its benign appearance lies a sophisticated attack capable of granting a remote actor complete control over a user's computer system. This is not a hypothetical scenario but a demonstrated reality, highlighting a severe, zero-click
Our Picks
