
Olivia Martainz
Security ConsultantOlivia Martainz helps organizations compile comprehensive enterprise security protocols. She shares his expertise with a global audience and provides real-world examples to help readers better understand the complexities of cybersecurity. Olivia covers endpoint detection and response solutions, zero-trust security principles, and emerging threats in enterprise security.
The rapid proliferation of sophisticated AI agents across corporate networks has introduced a formidable and stealthy security challenge, creating an environment where trusted automation tools can inadvertently become the most dangerous insiders. These AI systems, designed to streamline operations

The traditional image of a security guard standing motionless at a gate is rapidly fading into the background as data-driven intelligence becomes the primary engine of modern safety protocols. Today, the global security landscape is undergoing a profound transformation, moving away from static

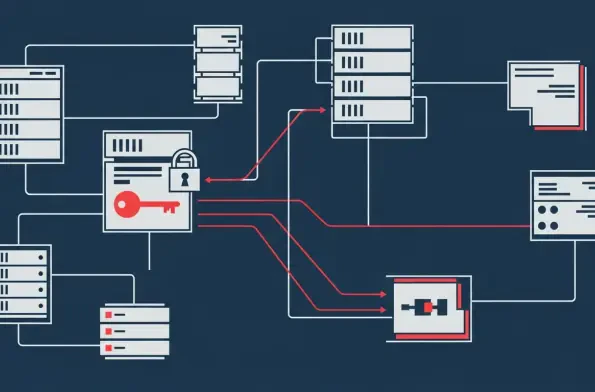
The implicit trust millions of people place in password managers as digital fortresses has been fundamentally challenged by a recent academic study that uncovered significant, exploitable flaws in their core security architecture. This research reveals a concerning disconnect between the advertised
With a deep background in threat intelligence and corporate security, Malik Haidar has spent his career on the front lines, dissecting the anatomy of sophisticated cyberattacks. Today, he joins us to unravel a particularly alarming campaign where a nation-state actor, UNC6201, exploited a
Vast troves of today's most sensitive encrypted data are being systematically stolen and stockpiled, not for immediate use, but to be unlocked by a key that does not yet exist. This strategy, known as "harvest now, decrypt later," represents a paradigm shift in data security, where

The digital ramparts protecting a nation's most sensitive information are not built of stone but of code, policy, and human vigilance, a reality that places Australia at a critical juncture in its ongoing cyber security campaign. Recent comprehensive assessments of the Commonwealth's

The digital extortion that once locked personal photos for a few hundred dollars has metastasized into a sophisticated criminal enterprise capable of bringing global supply chains to a standstill, demanding multi-million-dollar payments from the world’s largest corporations. This dramatic t

Our Picks
