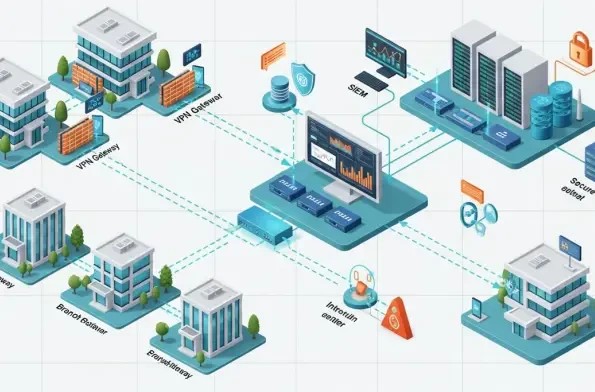
Maintaining the integrity of a secure perimeter requires constant vigilance because even the most trusted tools can harbor silent vulnerabilities that threaten to collapse an entire network’s availability. StrongSwan remains a cornerstone of the open-source security world, providing essential IPsec VPN capabilities for Windows, Linux, and macOS. However, the recent discovery of a high-severity Denial-of-Service (DoS) flaw has forced administrators to re-evaluate their current infrastructure. The release of the 6.0.5 patch is a critical step in addressing these security gaps, ensuring that enterprise tunnels remain functional and protected against remote disruptions.
Addressing Critical Security Gaps in Enterprise VPN Infrastructure
The identification of this vulnerability highlights a significant risk for organizations that rely on StrongSwan for stable connectivity. This flaw is not just a minor bug but a high-severity issue that directly impacts service availability by allowing remote attackers to disable the IKE daemon. Because StrongSwan is a versatile, cross-platform solution, the potential for widespread disruption is high if the 6.0.5 update is not applied promptly across all affected environments.
The Vital Role of StrongSwan in Modern Network Security
Open-source IPsec solutions serve as the backbone of encrypted communication, allowing data to traverse public networks within secure, private tunnels. StrongSwan provides the necessary framework for complex authentication, making it a favorite for large-scale enterprise deployments. However, the complexity of these protocols also makes them attractive targets for security researchers and malicious actors alike.
Authentication protocols like EAP-TTLS are particularly intricate, involving nested layers of data that require precise handling. When a flaw appears in the Internet Key Exchange (IKE) daemon, it creates a unique threat profile. Since this component manages the very establishment of secure sessions, a failure here can effectively lock out all authorized users from the corporate network.
Technical Breakdown of the EAP-TTLS Parser Vulnerability
1. Identifying the Integer Underflow in the AVP Parser: Step 1. Analysis
At the heart of the security advisory is a failure in how the software processes Attribute-Value Pair (AVP) data. The parser neglects to adequately validate the length fields provided within these data packets, allowing malformed inputs to pass through the initial checks. This lack of verification opens the door for crafted packets to manipulate the internal logic of the software.
Recognizing At-Risk Software Versions from 4.5.0 through 6.0.4: Part 1. Scope
Historical data indicates that this specific vulnerability spans a wide range of deployments. Specifically, any version of StrongSwan starting from 4.5.0 and continuing through 6.0.4 is susceptible to this parsing error. Administrators must check their current versioning to determine if their specific build is currently operating with this significant logic gap.
2. Mechanics of the Memory Management Failure: Step 2. Underflow
The technical trigger occurs when an attacker provides an invalid length value, specifically one falling between zero and seven. This input causes a 32-bit integer underflow within the parser’s logic. Because the system expects a positive value, the underflow results in an extremely large number that the software attempts to process as a legitimate size requirement.
The Risk of Excessive Memory Allocation and Segmentation Faults: Part 2. Crash
Once the underflow occurs, the software may attempt to allocate a massive amount of memory, quickly exhausting available system resources. In other scenarios, the logic error leads to a null-pointer dereference. Either outcome results in a segmentation fault, which causes the service to crash and stay offline until manually restarted or recovered by the system.
3. Understanding the Two-Phase Remote Attack Vector: Step 3. Exploitation
Researchers from Bishop Fox discovered that a successful exploit often involves a two-phase approach to ensure the daemon collapses. The methodology begins with a packet designed to corrupt the heap, followed by a second packet that triggers the actual crash. This sequence demonstrates a sophisticated understanding of how memory management interacts with protocol parsing.
Bypassing Authentication to Disable VPN Services Remotely: Part 3. Severity
The most alarming aspect of this vulnerability is that it can be exploited by an unauthenticated remote user. An attacker does not need credentials to send the malformed AVP data to the charon IKE daemon. This accessibility elevates the risk from a localized bug to a critical threat that can be launched against any exposed VPN gateway.
4. Deploying the Version 6.0.5 Security Patch: Step 4. Mitigation
To resolve these issues, the StrongSwan development team introduced version 6.0.5, which focuses on implementing rigorous input validation. This update ensures that the parser strictly checks all length fields before any memory operations or data processing take place. By hardening the boundary where external data enters the system, the developers effectively neutralized the underflow path.
Validating AVP Length Fields to Ensure Protocol Integrity: Part 4. Stability
The primary mechanism of the fix involves rejecting any AVP length that does not meet the minimum requirements of the protocol. This prevents malformed packets from reaching the deeper layers of the daemon’s logic. Ensuring protocol integrity at the entry point is the most effective way to maintain the stability of the VPN gateway under various network conditions.
Summary of Key Vulnerability Findings and Remediation
The investigation into StrongSwan revealed that versions 4.5.0 through 6.0.4 were fundamentally flawed in their handling of AVP data. The unauthenticated nature of the exploit made it a high-priority concern for NIST and the wider security community. It became clear that the only effective resolution for preventing these remote crashes was the immediate transition to the 6.0.5 release.
Broader Trends in Cryptographic Protocol Security
This incident reflects a wider industry trend where the complexity of authentication data becomes a liability if not matched by strict validation. As tunneling protocols evolve to support more diverse methods, the surface area for memory-related vulnerabilities naturally expands. The shift toward more aggressive input validation is a necessary response to the high-priority threats identified by cybersecurity oversight bodies worldwide.
Securing the Future of Remote Access Infrastructure
Network administrators who prioritized the deployment of the 6.0.5 patch successfully insulated their infrastructure from potential downtime. Moving forward, the focus turned toward conducting regular audits of daemon logs and staying informed about updates to the charon service. This proactive stance ensured that critical networking software was not left exposed to known logic errors. By adopting a cycle of continuous updates and monitoring, organizations maintained operational uptime and protected their remote access capabilities against the evolving landscape of cryptographic threats. These steps solidified the VPN gateway as a resilient point of entry rather than a single point of failure.