Malik Haidar is a seasoned cybersecurity veteran who has spent years in the trenches of multinational corporations, neutralizing sophisticated threats and outmaneuvering high-level hackers. With a unique professional DNA that blends deep technical intelligence with a sharp business perspective, he specializes in identifying the systemic cracks that traditional security measures often miss. His insights are particularly vital as we navigate an era where the rapid adoption of AI is colliding with legacy infrastructure, creating a new and dangerous frontier for digital identity.
Many organizations find that while their identity programs are maturing, overall enterprise risk is actually rising. How do “dark matter” applications—those legacy or siloed systems—create this paradox, and what specific metrics should security leaders use to measure the true extent of this unmanaged attack surface?
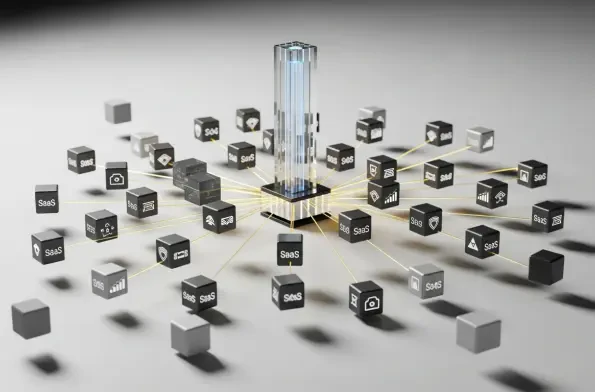
The paradox stems from a false sense of security where leaders believe that because their core systems are protected, the perimeter is safe, but “dark matter” applications—those hundreds of disconnected systems identified by the Ponemon Institute—act as invisible tunnels for attackers. These legacy and siloed SaaS tools exist outside the reach of centralized governance, meaning they don’t benefit from multi-factor authentication or real-time monitoring, yet they often hold sensitive corporate data. When an attacker finds these forgotten entry points, they can move laterally through the network with ease, completely bypassing the expensive IAM investments meant to stop them. To truly measure this, security leaders must look beyond simple uptime and focus on the “disconnected application ratio,” which compares the total number of apps in use to those integrated with the SSO. Additionally, tracking the “credential age” across localized accounts provides a sobering look at how many stale, unmanaged entry points are waiting to be exploited.
As autonomous AI agents and copilots enter the workforce, they often utilize localized accounts and stale tokens that bypass central governance. What are the immediate security implications of this behavior, and what step-by-step strategies can teams implement to ensure these agents don’t amplify existing credential risks?
The immediate danger is that AI agents are incredibly efficient at finding the path of least resistance, which in most enterprises is a siloed application using a stale token. Because these autonomous agents require high-speed access to perform tasks, they often skip the friction of modern security protocols, effectively acting as high-privileged users that security teams can’t even see. To combat this, teams must first perform a comprehensive discovery of “Shadow AI” to see exactly where these agents are interacting with disconnected systems. The next step is to implement a strict identity-first policy for all automated agents, ensuring they are assigned unique, short-lived credentials rather than piggybacking on old employee accounts. Finally, organizations need to move toward automated token rotation, removing the human element that often leads to credentials remaining active long after they should have been revoked.
Relying on manual password management and credential fixes often leads to significant audit friction and stalled digital initiatives. Why is this manual approach no longer sustainable against modern threats, and what tactical shifts are required to move from basic compliance to full operational control over every application?
Manual management is a losing strategy because it cannot scale at the speed of 2026’s threat landscape, where automated attacks occur in milliseconds while a manual credential reset takes minutes or even hours. When security teams are bogged down by the administrative weight of managing passwords across hundreds of fragmented apps, it creates a massive “confidence gap” and leads to audit friction that halts innovation. We need to move from a reactive “compliance checklist” mindset to proactive operational control by deploying automation that can bridge the gap between modern IAM systems and legacy apps. This tactical shift involves using identity orchestration tools that can programmatically enforce security policies even on applications that don’t naturally support them. By removing the manual burden, you not only satisfy auditors but also free up your talent to focus on high-level strategy rather than resetting forgotten passwords for a siloed HR tool.
Despite heavy investments in Zero Trust, the “last mile” of identity—including localized accounts and disconnected SaaS—remains a stubborn blind spot. What are the practical trade-offs when attempting to bring these outliers into a centralized system, and how can leaders close these gaps without disrupting employee productivity?
The primary trade-off is often between security rigor and user friction, as forcing a legacy system into a modern security framework can sometimes break existing workflows or slow down access for employees who rely on those tools. However, the risk of leaving these “last mile” gaps open is far too high, as they represent the most targeted and fragmented assets in the modern enterprise. To close these gaps without disrupting productivity, leaders should look for non-intrusive integration methods that act as a security overlay rather than a complete system overhaul. By utilizing technology that can automate the login process and manage credentials in the background, employees maintain their familiar speed while the organization gains visibility and control. It’s about creating a seamless bridge where the security layer is invisible to the user but provides the “Identity Maturity” required to defend against sophisticated exploitation.
What is your forecast for the identity threat landscape as we move toward 2026?
By 2026, I expect the traditional concept of a “human-only” perimeter to be completely obsolete, as autonomous agents will outnumber human users in many digital workflows. The biggest threat will be the “Identity Explosion,” where the sheer volume of non-human identities interacting with disconnected “dark matter” apps creates a playground for AI-driven malware. We will see a shift where attackers no longer target the front door of an organization but instead focus entirely on the fragmented edges—those siloed SaaS and legacy systems that were deemed “too hard” to secure. Organizations that fail to automate their identity governance today will find themselves unable to defend against the rapid-fire credential stuffing and token theft of the very near future. My advice for readers is to stop treating identity as a side project of the IT department and start treating it as the primary defensive line of the entire business. You must gain visibility into your disconnected surface area now, because if you don’t know an application exists, you can’t possibly protect it from the AI agents already looking for a way in.