Analytics Intelligence
Introduction The silent digital gateways that manage vast corporate networks often harbor the most significant security risks, a reality recently underscored by a series of critical vulnerability disclosures from a major software provider. The release of a new security update for Ivanti's
With a distinguished career spent on the front lines of corporate cybersecurity, Malik Haidar has a unique vantage point on the evolving threat landscape. Now, he's focused on a new and rapidly emerging frontier: the security of artificial intelligence systems. As businesses rush to adopt

In a stark reminder of the persistent threats facing digital ecosystems, Apple has issued emergency security updates across its product lines to neutralize a critical zero-day vulnerability that was already being exploited by attackers in the wild. The flaw, designated CVE-2026-20700, is a memory

The unchecked enthusiasm for AI-powered coding assistants is rapidly creating a dangerous blind spot in software development, where the rush for accelerated output directly generates a mountain of unseen vulnerabilities and long-term maintenance burdens. This breakneck pace of adoption, while
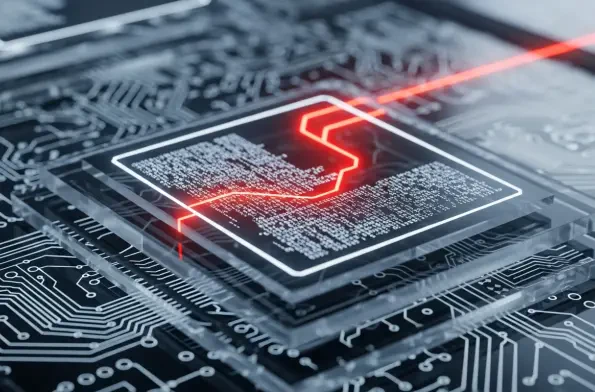
A startling discovery within a network of digital honeypots has provided definitive proof that threat actors are now successfully weaponizing Large Language Models to autonomously generate and deploy functional malware. Security researchers recently intercepted a malicious script that, while
The monthly ritual of software updates often feels like routine maintenance, but the latest security bulletin from Microsoft serves as a stark reminder of the persistent and evolving threats lurking in the digital landscape. February’s Patch Tuesday release addressed approximately 60 security f