The rapid shift toward microservices and containerized environments has rendered traditional perimeter-based firewalls almost entirely obsolete in the face of modern cyber threats. As organizations embrace these dynamic infrastructures, the security industry has pivoted from static analysis to active protection. Raven, a cybersecurity firm founded by veteran intelligence experts, has emerged from stealth with a $20 million investment to address these specific vulnerabilities. By focusing on the execution phase of software, the platform attempts to bridge the gap between development-time security and the unpredictable reality of live production environments.
The Evolution and Principles of Cloud-Native Security
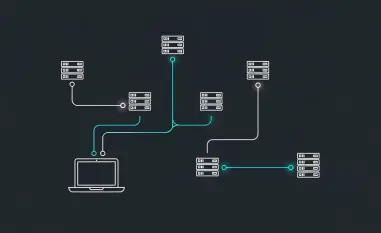
Traditional security models typically relied on “gatekeeping” by scanning code for known vulnerabilities before it ever reached the server. However, modern cloud architectures are far too fluid for this approach to remain effective alone. Cloud-native security has evolved to prioritize the runtime environment, acknowledging that even “clean” code can be exploited through zero-day vulnerabilities or sophisticated lateral movement within a cluster.
The core principle of this technology is the assumption that the environment is constantly changing. Instead of looking for a specific digital signature or a known bad file, these systems focus on the context of execution. This shift represents a transition from a reactive posture to a continuous monitoring state, where the security layer lives alongside the application rather than just at the entrance.
Core Pillars of Modern Runtime Protection
Real-Time Behavioral Analysis and Threat Mitigation
At the heart of Raven’s platform is a sophisticated behavioral analysis engine that monitors how code interacts with the underlying operating system. Unlike legacy tools that check files against a database, this system observes system calls, memory allocations, and network requests in real time. If a process suddenly attempts to access a restricted directory or initiates an unusual outbound connection, the platform can intervene instantly.
This level of granularity is crucial because it allows the system to catch zero-day exploits that have no existing signature. By defining a “baseline” of normal application behavior, the technology identifies anomalies that signify a breach. While this high level of sensitivity can sometimes lead to false positives, the speed at which it can neutralize a live attack is a significant improvement over manual incident response.
Automated Governance and Monitoring of AI Agents
As enterprises integrate artificial intelligence into their workflows, they inadvertently create new attack surfaces through autonomous AI agents. These agents often have the authority to modify code or access sensitive data, yet they frequently operate outside the direct oversight of security teams. Raven addresses this by treating AI agents as distinct entities within the cloud ecosystem, providing deep visibility into their logic and actions.
The platform monitors the “chain of thought” for these agents, ensuring that their outputs do not violate corporate security policies or introduce malicious configurations. This automated governance is a unique differentiator, as it prevents AI from becoming a “black box” that could be hijacked by external actors. It essentially acts as a supervisor for the digital workforce, maintaining administrative control over automated processes.
Emerging Trends in the Cloud Security Landscape
The industry is currently witnessing a massive consolidation of security functions into unified platforms known as Cloud-Native Application Protection Platforms (CNAPP). The trend is moving away from disparate tools toward integrated solutions that handle everything from posture management to active defense. Furthermore, there is a growing emphasis on “eBPF” technology, which allows security tools to run deep within the Linux kernel without slowing down the application, a method Raven utilizes to maintain high performance.
Practical Applications and Industry Implementation
In the financial sector, where rapid deployment is as vital as data integrity, this technology allows for the safe use of continuous delivery pipelines. For example, a bank might use runtime protection to ensure that a newly deployed microservice isn’t secretly leaking data through a supply chain vulnerability. Similarly, in healthcare, these tools protect sensitive patient records by blocking unauthorized access patterns at the container level, regardless of how the initial breach occurred.
Technical Obstacles and Market Limitations
Despite the promising capabilities, implementing deep runtime defense is not without its hurdles. One of the primary challenges is the “performance tax” — the computational overhead required to monitor every system call. If not optimized correctly, security tools can degrade application latency, leading to friction between security and engineering teams. Moreover, the complexity of managing these platforms requires a high level of expertise, which may limit adoption among smaller firms without dedicated security operations centers.
Future Projections for Autonomous Runtime Defense
The trajectory of this field points toward a future where security is entirely self-healing. We are moving toward a state where the defense layer not only detects and blocks a threat but also automatically patches the underlying vulnerability in the source code. This level of autonomy would drastically reduce the “dwell time” of hackers, making it nearly impossible for an intruder to maintain a foothold in a network for more than a few seconds.
Final Assessment and Review Summary
The emergence of sophisticated runtime protection marks a necessary turning point for enterprise cloud strategy. Raven’s focus on real-time behavior and AI oversight provided a robust framework for handling the complexities of modern software. While the potential for performance overhead remained a valid concern, the ability to mitigate zero-day threats in production offered a level of insurance that traditional tools could not match. Ultimately, the successful deployment of these systems became a prerequisite for any organization serious about maintaining a secure, automated cloud infrastructure.